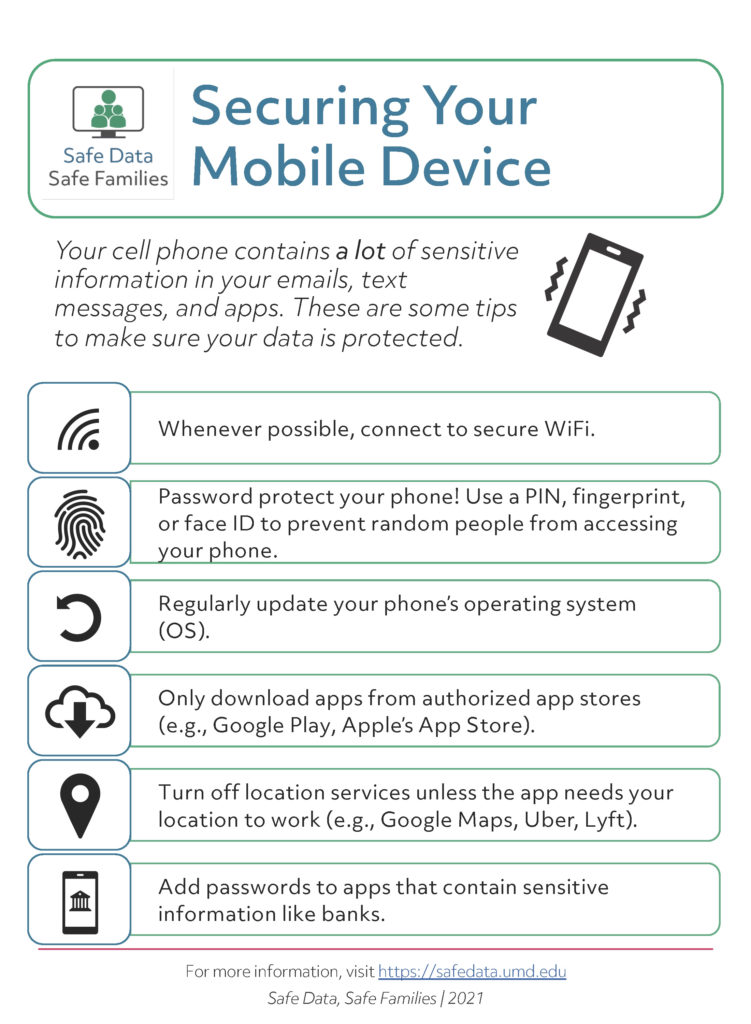
If you have a newer mobile phone or tablet, it’s likely storing a fair amount of sensitive data about you, including account access and passwords. Therefore, you should take steps to make sure that data is protected in case your device is lost or stolen. This handout includes a number of tips for keeping your mobile device secure, including the following.
- Nearly all phones and tablets now let you set up a password, PIN, and/or biometric authentication like your fingerprint or Face ID. Make sure this feature is turned on! Entering a PIN every time you pick up your device might feel annoying but it’s the best protection you have for your phone.
- Once you have a password for your phone, you may want to add a separate password for your most sensitive apps, like banking apps. Check the settings in individual apps to see if you can add a PIN. This means that even if someone gets access to your unlocked phone, they won’t be able to open those apps.
- Whenever possible, connect to a secure WiFi network. Many stores and public areas now offer free WiFi, but those networks are generally not secure. So if you are connected to public WiFi, it’s a good idea to avoid sending sensitive data.
- Whether you have an Android device, iPhone, or something else, the operating system gets regular updates, often because someone identified a security vulnerability in the system. Some phones let you auto-update, meaning the phone will download and install updates whenever they come through. Or you might get a prompt from the device to install a new update. This might seem annoying but it helps ensure your device keeps running without a problem and keeps it secure.
- Go through the device’s settings, especially privacy and location settings. A lot of apps request you share location data even though they don’t need it to work. You can control which apps get access to different types of data from your phone and when they can access it (e.g., only when the phone is in use).